Nowadays, one of the crucial nerve centers of military offensives resides in commanded UAV fleets and large numbers of drone units that are ready to attack, as well as engage in rescues and perform intelligence, surveillance and reconnaissance (ISR) missions to evaluate the enemies’ strengths and locations.

Photo of a General Atomics MQ-9 Reaper UAV in-flight.
The small weight and size of drones make them a powerful and seamless weapon — current military scenarios have proven that the use of drones during armed conflicts offers enhanced command and control over armies.
According to Research and Markets, the Military UAV Market was valued at $10.9 billion in 2019 and is projected to grow at a CAGR of 3.14% over the report’s forecast period and is projected to reach $14.8 billion by 2029.

Some of the reasons why combat drones have become popular are their flexible and adaptable capabilities, the main ones being reconnaissance as they are extremely accurate when engaged in surveillance missions.
Command and control is another of their strengths as they are able to accurately target an enemy’s position. The also identify and target attacks as well as detect potential targets. For logistics, drones can assist in delivering valuable supplies to the front lines as well as assisting in managing evacuations.
In order to unlock the potential of UAVs and their complete capabilities, their need for satellite communications (SATCOM) for a higher data rate to acquire Global Navigation Satellite System (GNSS) and Global Positioning System (GPS) are mandatory, as they provide a high degree of positioning accuracy for a variety of applications that include mapping, surveillance and search and rescue.
These on-orbit, constellation systems are composed of numerous satellites that can track positions on Earth at any time to assist warfighters.
UAVs can be equipped with radars and cameras to collect data and obtain geographic references as such is critical in knowing the exact position and time when UAV captures measurements or acquires photos.
When a drone communicates with its controller across radio frequency spectrums, an RF sensor passively listens to those frequencies. To identify the signal transmitted by a drone and its controller, the sensor identifies a communication protocol and compares that to a database of communication protocols.
Even though UAVs have revolutionized the military sector and war strategies, drones can also be interfered with, enabling an enemy to potentially command and control the drone as well as alter the unit’s position — or even provoke in- air collisions.
The drones available on today’s market have greatly improved their security to counter jamming attacks; however, there aren’t enough highly developed drones that rely on SATCOM and other technologies for control and navigation and that can actually withstand radio interference and GPS jamming.
The threat of GPS and GNSS jamming to military UAVs and satellite networks continues to grow — interference with a satellite network reduces the drone’s retransmission capabilities, such as the transmission of real time videos (one of the main advantages of drone fleets for military ops, as they are accurate and provide real-time images for rapid decision-making processes).
Beyond visual line of sight (BVLOS) and autonomous drone platforms require GNSS — the proliferation of inexpensive, readily available, jamming technologies endangers UAVs that are used for security, monitoring, reconnaissance, delivery, and other purposes.
As a GNSS satellite’s signal is an RF wave and loses power as the signal travels to the Earth’s surface, every transmission is inherently vulnerable to a variety of purposeful and inadvertent threats.
There are a few intentional techniques that are especially dangerous to military UAVs. These hostile capabilities can partially, or completely, block the reception of the target signal.
The jamming assault is a deliberate, interference technique, that involves the intrusion of RF signals that possess characteristics and higher power than the target signal.
Another deliberate interference technique is spoofing, wherein a device transmits a satellite-like signal at a higher power — the GNSS receiver starts to retrieve the false signal instead of the true signal. This causes the receiver to calculate a position or variable that is totally inaccurate.
The only way to combat interference is by acquiring the correct technologies to increase a UAV’s security and to ensure a resilient network.
UAV companies’ proprietary technologies to fight interference have not proven to be totally effective, as has been witnessed by the latest events with the ongoing European conflicts that have identified the potential threats for drones fleets.
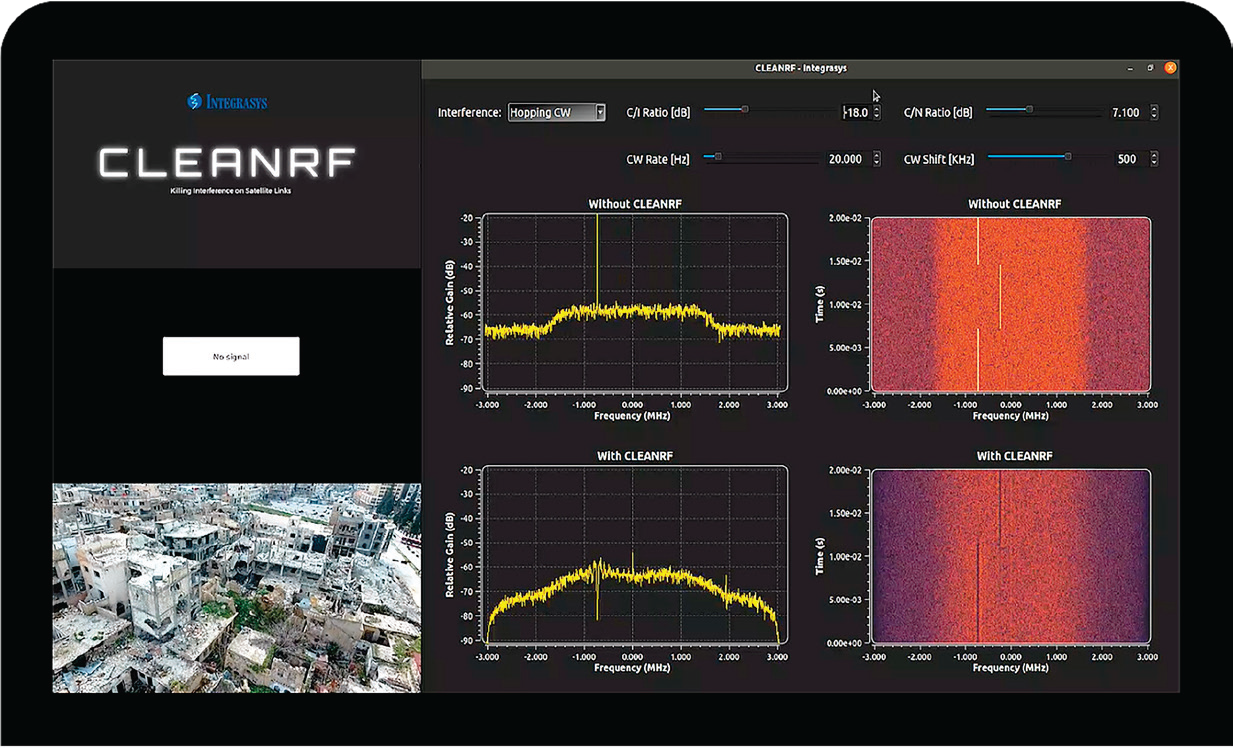
INTEGRASYS’ CLEANRF is the only technology that has proven to be a real defense against jamming and spoofing. In fact, this technology was awarded by the Mobile Satellite Users Association (MUSA) at Satellite Show 2022 as the ‘’Government Mobile Innovation 2022’.
The smart tool enables receivers or transceivers operating on satellite links to detect, identify, separate, and cancel RFI sources that impact the service signal.
The technology makes it possible for secure and reliable connections, while shielding the network terminals from the most frequent and dangerous sources of interference.

The newly developed interference canceler maximizes the amount of usable, clean spectrum by providing an intuitive, completely automated interface to address the most common and harmful interference issues.
Users who control crucial infrastructure, government resources, communications for security personnel, and so on, are typical users of this technology.

Alvaro Sanchez
Modern warfare demands viable technologies that will defend drone fleets and such technical tools need to be automated to assist in immediate implementation and that will be able to negate attacks on the crucial networks that are relied upon by today’s warfighters.
Author Alvaro Sanchez is the Chief Executive Officer of INTEGRASYS.
www.integrasys-space.com

